I tried out to look at some signals that use KG-84 encryption (based on Saville algorithm) in order to identify its footprint inside them and differences (if any), specifically: the two NATO widely used waveforms STANAG-4285 and STANAG-4481-FSK, one of the STANAG-4285 variants (this one possibly a Croatian version) and the FSK 600Bd/400Hz by Turkish Military. Since only four waveforms, this does not claim to be a complete view, rather it will be updated as soon as I'll get other such encrypted signals.
-
Given a signal, as previously seen, the existence of KG-84 encryption can be detected by its well-known 64-bit sync pattern that is inserted at the beginning of each session/message and followed by the encryption initialization:
1111101111001110101100001011100011011010010001001100101010000001
In order to highlight the sync pattern we need to work with bitstream files, also known as ASCII-bits file, containing only the binary symbols 0 and 1 and provided by decoders such as k500 or Sorcerer (in the picture belows). This because - for example - the PSK-8 demodulated output from signals analyzers such SA, provide on-the-air symbols that still contains extra-symbols due to FEC and they should de-scrambled, de-interleaved and converted from HEX values to binary.
The bitstream analysis is performed using a bit flow processor and editor.
The bitstream analysis is performed using a bit flow processor and editor.
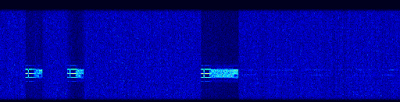
STANAG-4481P (STANAG-4285 300bps/L)
in this case the sync is followed by a 512 bits group consisting of two 64 bits sequences repeated 4 times: the two 64 bits sequences form the 128 bits key, k500 call them as "inizialization vectors" and are clearly indicated in its output as two strings each of 32 HEX characters. As far as I can see, both the sync and the key are inserted at the beginning of the session and are not re-inserted or repeated so that the message can not be deciphered in case of late entry.
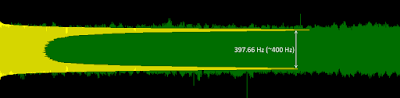
STANAG-4481F (FSK 75Bd/850)
 |
| pic. 2 - NATO STANAG-4481-FSK |
since the same operating environment (NATO), STANAG-4481-FSK adopts the same structure as in 4285. It is worth noting in pic. 3 that the 64-bit sync patterns produce ~850ms ACF spikes visible in the initial part of the signal.
 |
| pic. 3 - 850ms ACF spikes due to key insertion |
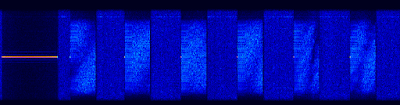
STANAG-4285 variant
 |
| pic. 4 a STANAG-4285 variant |
although it's compatible with NATO S-4285, this waveform (the user is suggested to be Croatian) does not provide KG-84 encryption (coud not find the sync pattersn) but rather a sort of linear encryption taht is not detected by the standard S-4285 decoders such as k500 and Sorcerer.
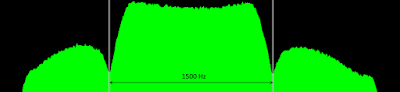
Turkish FSK 600Bd/400Hz
 |
| pic. 5 - the Turkish FSK/600/400 |
for what concerns KG-84 encryption, this waveform exhibits an interesting peculiarity: the sync pattern is not followed by the 512-bits key block as seen in NATO 4285 and 4481 implementations. I do not know if the 128 bits immediately following the syncr are indeed the key or else the key is obscured to standard decoders.
As expected, since this trasmission consists of 7 blocks, the sync is repeated 7 times each 3954 bits exactly: since the apparently lack of the key I don't know if the transmission carries seven distinct messages or if the repetion is an help in case of late entry (so the messages are the same?).
 |
| pic. 6 - the seven resolvers |
It's quite useless and waste of space and bandwidth to list here concepts and images that are easily found on the web about KG-84, below just few links:
Thanks to my friend KarapuZ for pointing me this argument and his stimolous to deepen.